Most of us have seen the scam attempt emails and wonder why they even try because they are obviously fake. However, we’ve been seeing a rash of phishing (pronounced fishing) emails that are getting trickier to identify. These emails mimic the look and feel of notifications coming directly from the Office 365 system.
Why are these emails more and more prevalant? Because people are taking the bate and getting scammed. We’ve seen issues recently where users think they are following directions from the administrator, but are opening themselves up to a world of trouble. In our most recent encounter, the scammer used their phishing email to obtain the username and password of the targeted user. They used those credentials to log into their Office 365 account without the users knowledge. Then they set up mail rules to hide their activity and started spamming people from the users account. On top of this, they were using mail forwarding rules to monitor received emails. Using all this, they were watching inbound messages and injecting their own scam attempts into legitimate email conversations. In our example, a financial transaction was being discussed without any details and the scammer decided to respond to the vendor with bank account information that would have funneled funds into their own account. That’s just dirty! The vendor was smart and noticed some things looked off and contacted the client who in turn contacted us.
We were able to get things cleaned up and thankfully nothing was stolen, but here are some quick tips to identify if an email is legitimate or if it’s an attempt to go phishing:
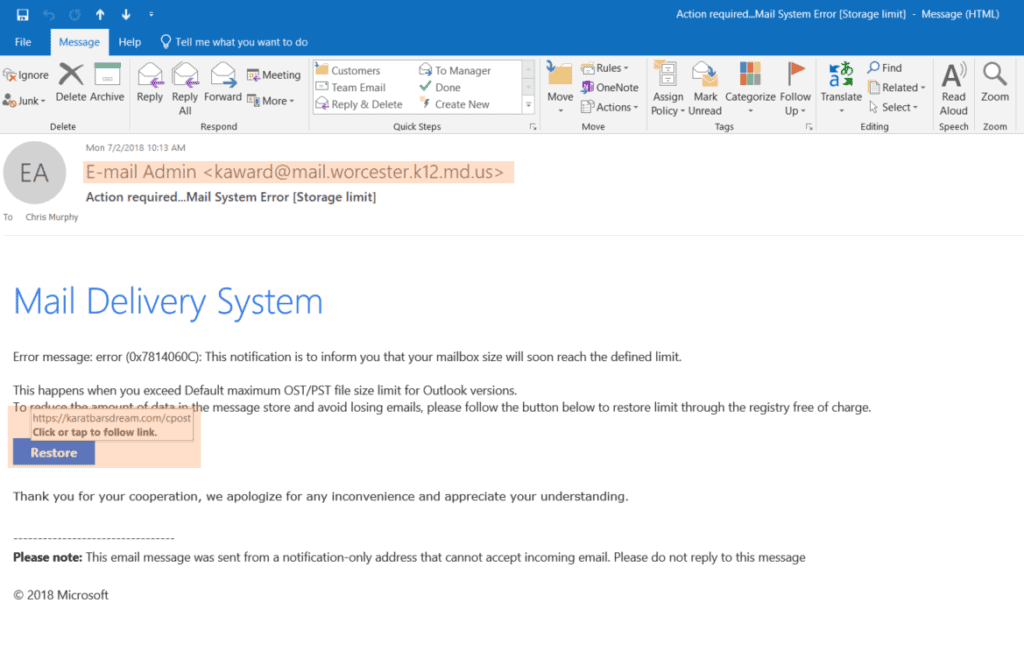
- Look at the from email address — If the email address looks odd or isn’t someone you are familiar with, it’s probably spam.
- Check the address of links in the email body — If you hover over the links of an email without clicking on them, a box will pop up with the full address. If it looks like a bunch of gibberish or isn’t a trusted address, don’t click it. When in doubt, contact your network administrator.
What additional steps can you take to secure yourself or your business?
- Use strong passwords — Use a minimum of 8 characters use a mixture of uppercase, lowercase, numbers, and symbols. Avoid using sequential numbers, like ‘123’, or common words, like ‘password’. Google has a good article about creating strong passwords here: Create a Strong Password
- Implement email spam/virus filtering — Email spam filtering is a good line of defense that will check the validity of the sender as well as scan the email for malicious content
- Turn on two-factor authentication — This sends a code to your phone and won’t let you log in without the correct password and authentication code
Published on July 2, 2018

